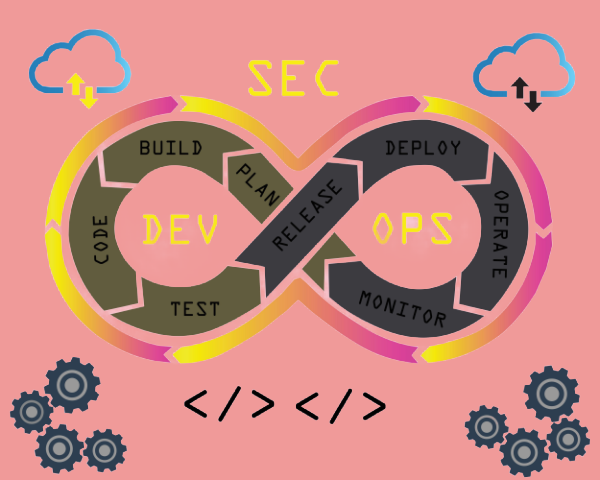
DevSecOps is integrating security coding practices into DevOps. Making security a shared responsibility.
The core principle in Implementing security into DevSecOp is SHIFT SECURITY LEFT
Shift left is introducing security as early as possible in the Software Development Lifecycle (SDLC).This approach aims to find and fix vulnerabilities when they are cheapest and easiest to address in the code itself rather than discovering them in production like Imbed SAST (Testing code in development)every aspect of software dev cycle.
Implementing Security practice in DevSecOps team , – imbed Application security such as AST, SAST,DAST, IAST, SCA.
Application security Testing:
| In Dev | Integration | Acceptance Stage | Pre-production | Production |
| SAST | SCA | SAST, DAST,MAST | SAST, DAST,MAST | RAST |
| SCA | IAST | IAST |
Best Practices for Implementing Secure coding practice
- Emphasize to integrate security into every aspect of SDLC.
- Test internal interfaces – API, UI.
- Test Often.
When SAST is implemented in development, The DevSecOps are able to determine the security gaps, Broken path, Expected output, loop tests and data flow.It exposes all these to DevSecOps.
Implementing Secure coding practice
- SAST implementation
- API Test – validation testing, UI testing, functional testing- API functions | API Business logic | Input validation. | error handling | load testing(API performance(Jmeter) .
- API Security – Input Validation, Headers(dev) . XSS,CSRF, BOLA, Broken Function Level Authentication, (in DevSecOps)
- Agile SDLC for continuous feedback and testing.
Integrate Secure coding practice in DEV
- Code review & Quality Assurance (potential vulnerability)
Quality Assurance is testing the software that it meets desired quality standards (testing, bugs tracking, features, continuous improvement).
2. Threat Modelling and Vulnerability Assessment (security approach -Mitigation Strategy)
Threat Modeling can be either STRIDE or OWASP top 10
3. Implement SAST.-
4. Implemt secure configuration mangement.
5. Cross functional team
How to deal with Resistance to change in Development
- Address resistance to change, involve stakeholders in decision making
- provide training and support
- Agile
- Encourage Accountability and ownership
- Overcome security-slowing misconceptions.
Secure SDLC Phases
- Requirements & Design : Threat Modeling
- Development (Code):
- Secure Coding Training & Standards: Developers are trained on secure coding best practices (e.g., OWASP Top 10
3. Build (Continuous Integration – CI):
- Static Application Security Testing (SAST): Automated tools that scan the application’s source code, bytecode, or binary without executing it. SAST is excellent at finding certain classes of vulnerabilities like SQL injection, buffer overflows, and insecure cryptographic usage.46
Software Composition Analysis (SCA): Tools that identify all open-source and third-party components in an application and check them against a database of known vulnerabilities (CVEs). Given that modern applications are largely composed of open-source libraries
4. Test (Continuous Delivery – CD):
Dynamic Application Security Testing (DAST): Automated tools that test the running application from the outside-in, simulating attacks against its interfaces (web pages, APIs). DAST is effective at finding runtime and configuration issues that SAST might miss
Interactive Application Security Testing (IAST): A hybrid approach that combines elements of SAST and DAST. It uses an agent instrumented within the running application to monitor its internal behavior while DAST scans are performed, providing more accurate results with fewer false positives
5. Deploy & Maintain (Production):
- Container Image Scanning: Scanning container images for known vulnerabilities in the OS and software packages before they are deployed to a registry or runtime environment.
Continuous Monitoring & Alerting: Using security tools in production to monitor for active threats, anomalies, and new vulnerabilities, and feeding this information back into the development lifecycle